
Computex 2012: Lian Li Want To Sell You A Train, Or A Case with 26 3.5” HDD Slots
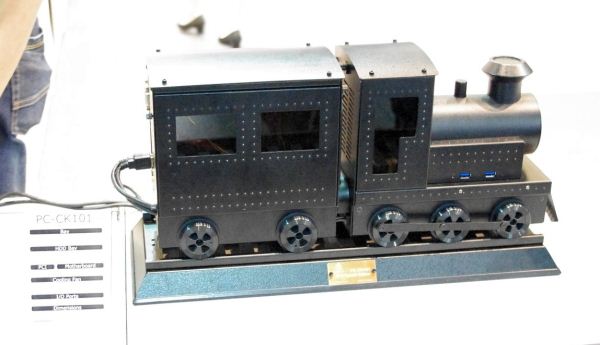
Visiting the Lian Li booth is always interesting. Last year we saw the TU-200 mini-ITX case aimed at taking a gaming machine with you on the move. This year, we get trains.
The PC-CK101 is a limited run product which looks like a train but will fit inside a mini-ITX motherboard with a couple of SSDs and appropriate power. On the case are a couple of USB 3.0 ports, and there is even room for a slim optical drive behind the cow catcher. The model on display was accompanied with a version of the case that had been outfitted with an engine and had fully moving parts along a track.
Also on the Lian Li booth we were introduced to the PC-D8000. A double width and tall case designed to fit HTPX motherboards as well as twenty-six 3.5 inch hard drives (6 of them in hotswappable bays).
This case looks like it would be great for organising a 4 dual radiator water cooling setup (the top has panels which can be switched with a dual 120mm fan slots), with plenty of space for organisation. Or, as I suggested, a modder may adjust the case to fit two motherboards and two systems – one system for low powered usage (word processing, email, internet), and a second system for gaming.
Also on display was the PC-V650, a mATX version of the PC-Q09B, and the PC-V750WX, a normal height E-ATX case. LianLi also showed me the PC-X2000FN, a very tall case which is only slightly wider than a motherboard, with space above and below for hard drives.
Mini-ITX cases are also the order of the day, with LianLi having their vertical power supplied PC-Q02 and PC-Q03.
Read More ...
Update: CERT/CC Takes AMD To Task On Driver Security, AMD Responds
In a bit of an odd move, the Carnegie Mellon's Computer Emergency Readiness Team (CERT/CC) has posted a vulnerability report and a blog post taking AMD to task over their drivers and the impact on system security. As the major partner in the United States’ internet security agency US-CERT and de-facto coordinator for the international CERTs, CERT/CC is both a front-line organization for developing responses to cybersecurity threats and on a more typical day is responsible for organizing and publishing reports and notices about computer system vulnerabilities. So while it’s common for CERT/CC to publish information regarding specific vulnerabilities, it’s less common for them to get involved with general security weaknesses in this manner.
So what has drawn CERT/CC’s attention? It turns out that AMD’s drivers don’t properly behave with/support a vulnerability mitigation feature called Address Space Layout Randomization (ASLR). ASLR serves to make it harder for software vulnerabilities to be exploited by randomizing certain program structures in memory, so that the addresses of these structures cannot reliably be predicted and attacked. Although not undefeatable, ASLR can reduce a number of different types of attacks from a system-owning exploit into a program crash that keeps the system secure. In other words ASLR can’t fix the underlying vulnerabilities in programs, but it can help mitigate the problem so that a proper fix can be instituted.
Because of the chaotic nature of ASLR not every program (particularly legacy programs) can work with it, and for that reason since its introduction in Windows Vista in 2006 ASLR has been a per-program feature that is only enabled with applications that are flagged as being compatible. However because most applications can handle it just fine, systems requiring higher security can use the Enhanced Mitigation Experience Toolkit (EMET) to enable ASLR across the system, which forcibly activates ASLR for all programs.
It’s this last bit that has caught CERT/CC’s attention. As it stands AMD’s video drivers are not ASLR compatible. Turning on ASLR will cause AMD’s drivers to crash, making always-on ASLR unusable on systems using AMD’s drivers.
From a practical perspective this isn’t an issue that affects more than a handful of users. Unlike DEP it’s not something that can be turned on from within Windows, so even technical users like ourselves almost never have ASLR in always-on mode. However for governments and other high value institutions this means they’re forced to choose between AMD hardware and ASLR, which is not something they want to be worrying about. Furthermore it’s been the long-standing goal of computer security organizations to get OSes and programs to a state where ASLR can be enabled globally for every user, a very messy transition that is held back by programs and drivers that are still not ASLR compatible.
Drivers in turn are of particular concern here because of how they interact with the Windows kernel, with video drivers in particular having high access levels for performance purposes, a position that will only become more entrenched as GPUs continue to become more CPU-like and more important to even fundamental computing. All of this is compounded by the fact that AMD in has already been in the spotlight for security vulnerabilities as their drivers were found to have a security exploit in 2007.
Ultimately CERT/CC is looking to apply pressure to AMD to get them to finally make their drivers ASLR compatible, even going so far as to specifically testing and naming Intel and NVIDIA as having ASLR compatible drivers in the vulnerability note. Because of their relationship with US-CERT this is akin to having an arm of the US Government breathing down your neck, which does tend to get results, doubleplus so since the US Government is also a massive IT buyer. In the meantime typical computer users have nothing to be concerned about – and this is the important part for most of us – but it’s unfortunate that AMD has let themselves end up in this situation in the first place.
Source: Slashdot
Update: CERT/CC contacted us this afternoon to clarify who originated the vulnerability report in question. It is technically CERT/CC who published it (in spite of it appearing on US-CERT), so we've corrected the article accordingly.
Update 2: AMD has issued a formal statement in response to CERT/CC's report. In it they assert that the specific condition CERT/CC specifies (modifying a registry key) was not reported in advance, and go on to reiterate that regular users (even those using EMET) are not impacted by this. Furthermore AMD states that they are working on a driver that corrects the issue CERT/CC has discovered. We have republished the full response below
CERT recently approached AMD with information pertaining to what they believed to be a possible video driver vulnerability exposed by non-default settings of the Microsoft Enhanced Mitigation Experience Toolkit (EMET). EMET is a security test tool that allows system administrators to create test conditions to validate correct behavior of system components or indicate potential weak points. The presence of an issue does not necessarily mean that this issue can be exploited in regular operation of a system. The default safety settings of the EMET do not cause the issue in question to occur.
The non-default settings used to produce the system crash at start-up as reported by CERT require changing a System Registry key for the tool (named "EnableUnsafeSettings"), which was not documented until the CERT report was published, and is not accessible through the EMET tool itself.
Given that the conditions created by CERT are a departure from the default safety settings of the Microsoft EMET, users of AMD graphics products will face the problem outlined by the CERT report if their EMET settings are modified, and will otherwise not experience the issue in question. Shortly, AMD will release a driver designed to ensure that a crash does not take place under the conditions outlined by CERT.
Read More ...
Transportation Secretary LaHood Reveals “Blueprint for Ending Distracted Driving”
The California and Delaware programs will test out increased law enforcement and public education campaigns for distracted driving
Read More ...
Best Buy Founder/Chairman Resigns 1 Year Early
He is also looking at possible options for his 20.1 percent stake in Best Buy
Read More ...
Samsung Sues Aussie Patent Office; Prospect of U.S. Galaxy S III Ban Grow
Global legal war between Apple and Samsung remains far from over and damage may soon escalate
Read More ...
Available Tags:HDD , AMD , Driver , AMD , Samsung , Galaxy ,













No comments:
Post a Comment